Reducing Attack Surface using CloudFront VPC Origins
Sumit Kumar Dubey
6 min read
When designing secure internet-facing applications in AWS, one principle should guide the architecture:
The origin should never be directly exposed to the internet.
For years, teams placed CloudFront in front of an internet-facing Application Load Balancer (ALB) and used header validation with automated secret rotation to prevent origin bypass.
It was a well-engineered pattern. But it still relied on protecting a publicly exposed load balancer.
With VPC Origins in Amazon CloudFront, AWS introduced a fundamentally stronger model:
Keep the origin private and let CloudFront connect to it from inside your VPC.
This article compares two architectures and explains why VPC Origins represent a structural improvement in cloud security design.
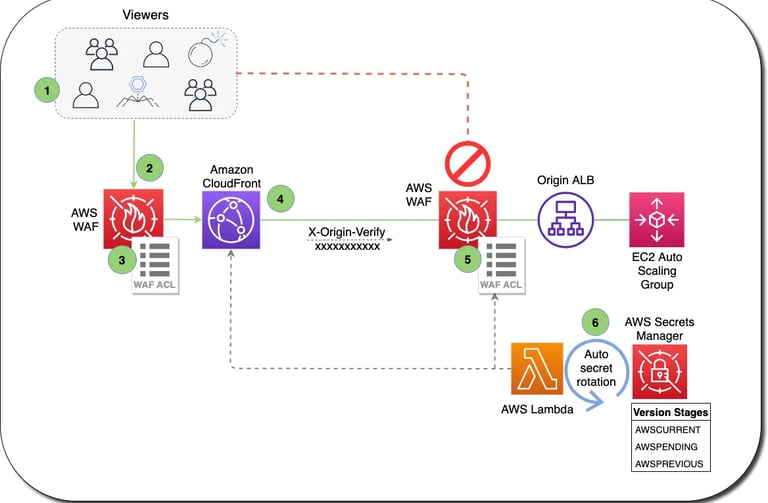
Architecture 1: Public ALB Protected by Header Validation
In the traditional model, the architecture looks like this: User → CloudFront (+WAF) → Internet-Facing ALB (+WAF) → Backend
In this model, the Application Load Balancer is internet-facing and has a publicly resolvable DNS name. That means anyone could attempt to send traffic directly to it, bypassing CloudFront. To prevent that, teams implemented layered controls.
How the Protection Works
CloudFront injects a custom header (e.g., X-Origin-Verify) into origin requests.
The ALB listener validates the header.
Requests without the correct header are rejected.
The header value is stored in AWS Secrets Manager.
A Lambda function rotates the secret automatically.
CloudFront and ALB configurations are updated accordingly.
This is not a manual system but rotation can be fully automated and production-grade.
In addition to header validation, many teams also restricted the ALB security group to the CloudFront origin-facing prefix list. However, this prefix list is not distribution-specific. It represents IP ranges used by CloudFront infrastructure globally.
This means:
It does not guarantee traffic is from your specific distribution.
It does not enforce account-level isolation.
It only restricts traffic to CloudFront infrastructure and not to your deployment alone.
Because the ALB was still internet-facing and publicly resolvable, prefix filtering alone was not sufficient. Header validation remained necessary to prevent bypass.
Strengths of This Model
Automated secret lifecycle management
Mature and proven pattern
Works well with edge-based WAF
Strong access control logic
This architecture is not insecure. It is layered and well-engineered but it has structural limitations.
Structural Limitations
Public Exposure Still Exists:
Even with header validation:
The ALB is publicly reachable.
DNS resolution is public.
The resource is exposed at the network layer.
Security depends on filtering traffic, not eliminating exposure.
Dependency on Shared Secrets:
Even with automated rotation:
Secret synchronization must remain consistent.
Configuration drift can cause failures.
The system relies on header validation logic.
More moving parts increase operational complexity. Operational drift can introduce failure risk.
Expanded Attack Surface: Because the ALB has a public endpoint:
It can be scanned
It can be targeted
It increases the externally reachable footprint
This is security by validation and not by isolation.
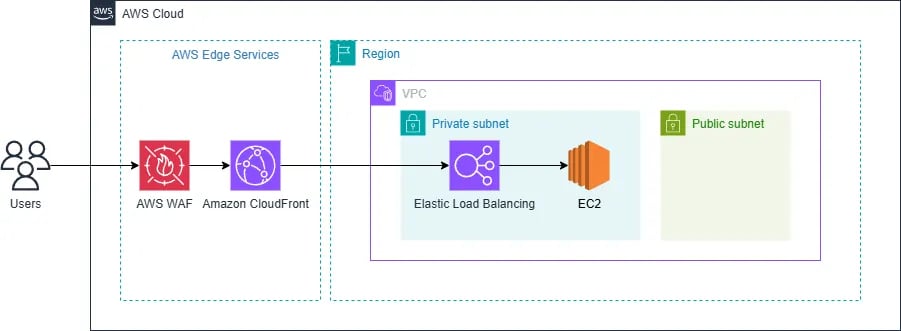
Key differences:
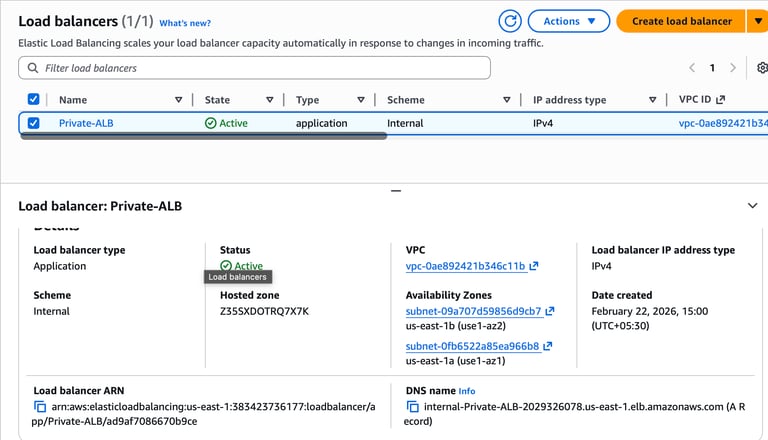
The ALB is internal
No public IP
No public DNS resolution
No internet route to origin
CloudFront connects privately inside your VPC
CloudFront provisions managed ENIs inside your selected subnets and connects to the ALB over AWS internal networking.
How VPC Origins Actually Work
When you configure a VPC Origin in CloudFront:
CloudFront provisions service-managed Elastic Network Interfaces (ENIs) inside the subnets you select.
These ENIs exist inside your VPC.
Traffic from CloudFront to your ALB originates from those ENIs.
Communication happens over AWS private networking.
This is not public internet traffic. This is not based on public CloudFront IP ranges. The connectivity boundary shifts inside your VPC.
Important: No Need for WAF at the ALB
In the VPC Origin pattern:
The ALB is not internet-facing.
No direct public traffic can reach it.
All internet traffic terminates at CloudFront.
Therefore, AWS WAF should be attached only at CloudFront and not at the ALB.
This avoids:
Duplicate rule management
Additional cost
Unnecessary inspection layers
Security inspection belongs at the edge. The origin remains private and simplified.
Why Prefix Lists Are No Longer the Core Control
In the internet-facing ALB model, you often had to allow:
That prefix list represents CloudFront infrastructure IP ranges globally and is not distribution-specific.
In that older model:
Prefix filtering alone was insufficient.
Header validation was required.
The ALB remained public.
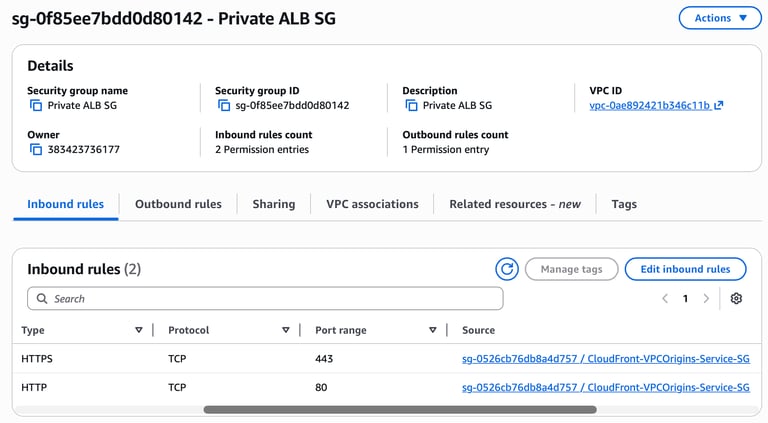
In the VPC Origin model:
The ALB is internal.
Traffic originates from ENIs inside your VPC.
You restrict access using security group referencing (allowing the CloudFront-managed ENI security group).
You are not relying on global public IP prefix lists as the primary control.
The primary security boundary is now private network isolation.
Step-by-Step Implementation
Step 1: Deploy an Internal ALB
Create an Application Load Balancer.
Select Internal scheme.
Place it in private subnets.
Attach target groups.
Ensure:
No public IP association.
No internet-facing configuration.
Step 2: Configure Security Groups
Identify the security group used by CloudFront-managed ENIs.
Allow inbound traffic to the ALB from that security group.
Do not allow 0.0.0.0/0.
Do not make the ALB internet-facing.
The trust boundary is now VPC-local.
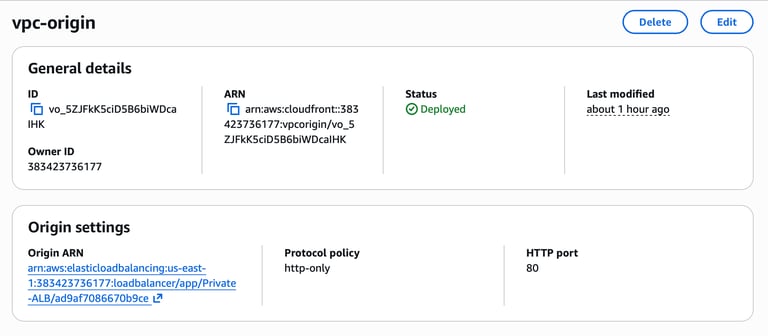
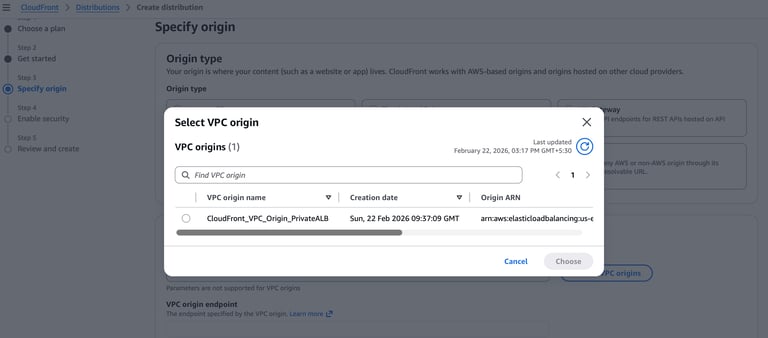
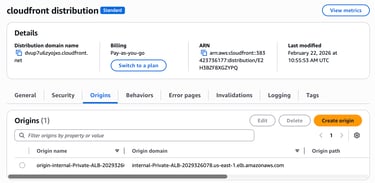
Step 3: Configure VPC Origin in CloudFront
In CloudFront:
Add a new origin.
Choose VPC Origin.
Select the internal ALB.
Choose the configurations.
Review and Create
CloudFront automatically provisions ENIs and establishes private connectivity.
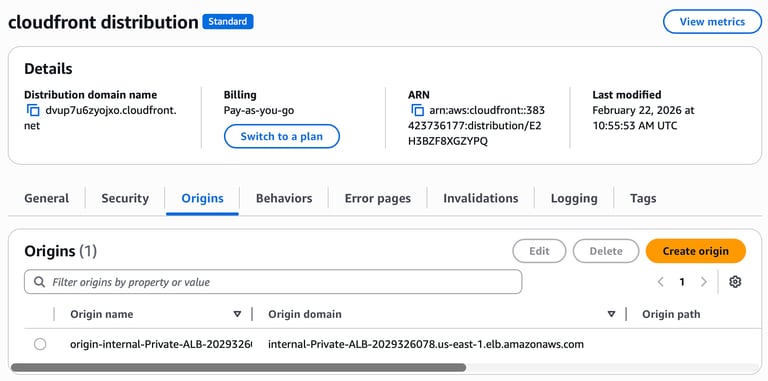
Step 4: Attach the VPC Origin to a CloudFront Distribution
CloudFront automatically provisions ENIs and establishes private connectivity.

Step 5: Attach WAF at CloudFront
Attach AWS WAF to the CloudFront distribution.
This ensures:
All public traffic is inspected at the edge.
No inspection is needed at the origin.
Centralized policy enforcement.
Architectural Comparison
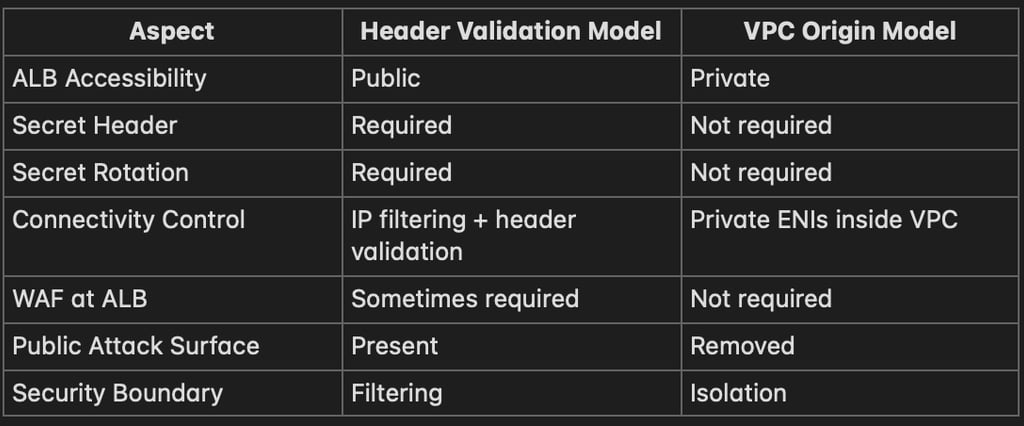
Final Thoughts
The traditional header-validation model remains technically sound and suitable for legacy deployments.
However, when designing new workloads today, VPC Origins offer:
Reduced attack surface
Elimination of secret dependency
No need for WAF at ALB
Cleaner operational model
Better alignment with Zero Trust principles
Security becomes a property of your architecture, not a mechanism layered on top of exposure and that is the real advancement.
IMPORTANT UPDATE: Cross-Account Support for CloudFront VPC Origins
AWS has announced support for cross-account VPC origins, allowing you to host VPC origin resources (like internal ALBs, NLBs, or EC2 instances in private subnets) in one AWS account while using them from a CloudFront distribution in a different account. This is facilitated using AWS Resource Access Manager (RAM) and enables teams to maintain multi-account security boundaries while still benefiting from the private origin model of CloudFront.
Even with cross-account support, the core principle remains the same — CloudFront still connects privately through managed infrastructure to the origin, and the origin remains hidden from the public internet. The enhancement simply enables this architecture to function across organizational boundaries, improving flexibility and security in multi-account environments.
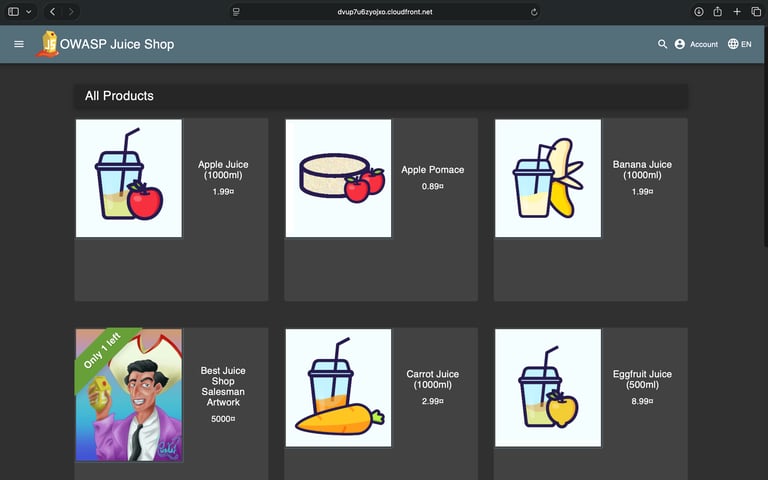
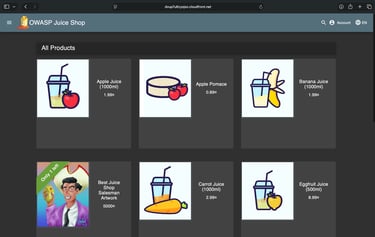
Application Accessed via CloudFront (Origin Remains Private)
The screenshot below shows the application being accessed using the CloudFront distribution domain. The backend Application Load Balancer is internal and not directly reachable from the internet. All public traffic terminates at CloudFront.
Conclusion
In this blog, we explored the evolution of origin protection in AWS, from using header validation with automated secret rotation on internet-facing load balancers to adopting the VPC Origin pattern in CloudFront. While the traditional approach is technically sound and production-ready, it still protects an origin that remains publicly exposed at the network layer.
With CloudFront VPC Origins, the architecture shifts from filtering and validation-based security to network-level isolation. By keeping the Application Load Balancer internal and allowing CloudFront to connect through service-managed ENIs within the VPC, public exposure is eliminated entirely. This reduces attack surface, simplifies operational overhead, removes dependency on shared secrets, and aligns more closely with modern Zero Trust principles.
Designing systems that are private by default is always stronger than protecting systems that are publicly exposed. The VPC Origin model enables exactly that: a cleaner, more secure, and architecturally robust way to protect backend applications in AWS.
Disclaimer
This blog provides architectural guidance on implementing CloudFront VPC Origins and comparing it with traditional header-validation-based origin protection. AWS environments, networking configurations, and security requirements may vary across organizations.
While the VPC Origin model reduces public exposure and simplifies origin security, implementation details such as subnet design, security group configuration, IAM permissions, and multi-account setups must be carefully reviewed and tailored to your specific environment.
Before deploying this architecture in production, thoroughly test the configuration in a staging or development environment. Validate connectivity, security boundaries, logging, monitoring, and compliance requirements according to your organizational policies.
The information provided in this article serves as a technical reference and architectural perspective. Final implementations should align with your security standards, governance policies, and operational objectives. Always perform due diligence and seek expert consultation where necessary.
Architecture 2: Internal ALB with CloudFront VPC Origin
With VPC Origins, the architecture becomes: User → CloudFront (+ WAF) → Internal ALB → Backend
Daily Ink Well
© 2024. All rights reserved.
